The Invisible Front: How Iran’s Cyber War Reaches Your Hospital, Bank, and Home

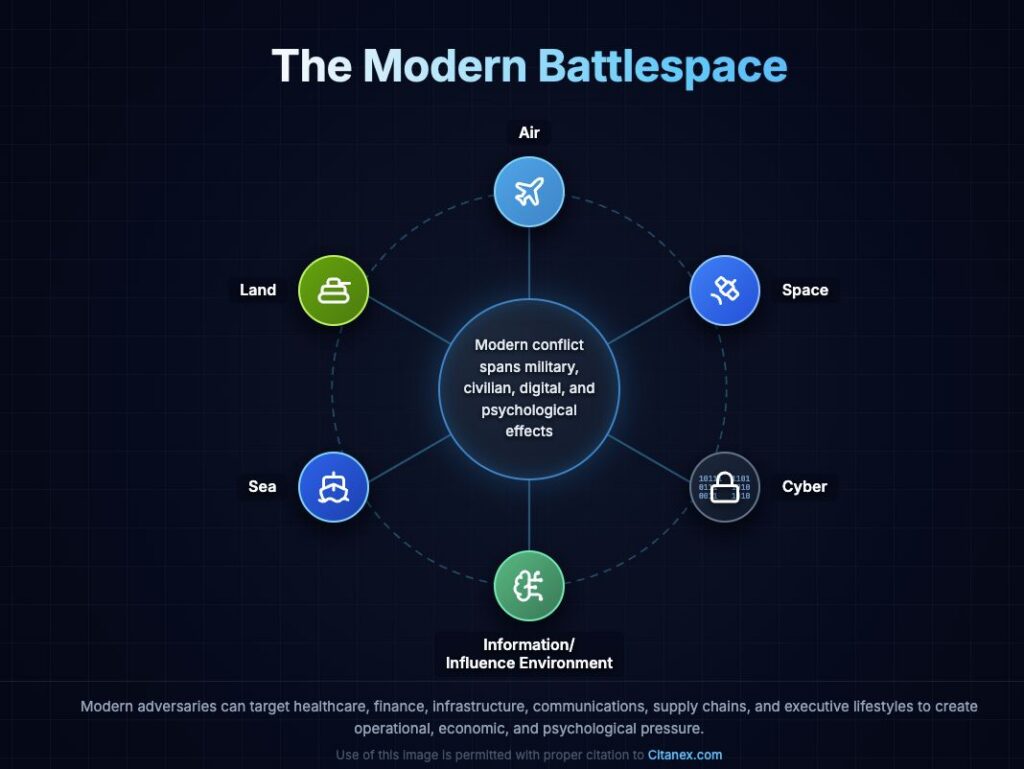
The Iran cyber threat in 2026 has fundamentally changed the rules of modern conflict. Today’s battlespace spans land, maritime, air, space, cyber, and the information environment — and cyber operations are now fully embedded in military, economic, and psychological pressure campaigns.
That matters now because the expanding U.S.-Iran war is not simply a conventional military contest. In reality, it is a multi-domain confrontation. Retaliation arrives through cyberattacks, supply-chain attacks, hits on critical systems, and pressure against civilian sectors. Ultimately, these sectors hold up public confidence and economic stability.
Estimated reading time: 10 minutes
49,238 hits
How the Iran Cyber Threat Has Changed the Modern Battlespace
Traditional military training often begins with the classic domains of warfare: land, sea, and air. Those domains remain central. However, modern conflict increasingly turns on the ability to disrupt the systems that sustain military power. In other words, communications, logistics, finance, and public perception are now targets too. As a result, space-based assets, cloud systems, telecom networks, data centers, and identity platforms are now part of the active battlespace.
For Iran and Iran-linked groups, this creates a key strategic advantage. Specifically, Tehran does not need to match the United States weapon-for-weapon to cause real damage. For organizations tracking the Iran cyber threat, this creates a new kind of exposure that goes far beyond conventional defense. For example, hospitals, banks, water systems, energy networks, remote-access tools, and third-party vendors are all viable entry points.
The Iran Cyber Threat to U.S. Hospitals and Healthcare Systems
Healthcare is one of the most attractive targets in any cyber campaign tied to global conflict. It sits at the intersection of public safety, patient care, supply-chain fragility, and public trust. For that reason, hostile groups return to it again and again.
A current example is the attack on U.S. medical device maker Stryker, where the Iran-linked group Handala claimed credit. The point here is not simply the incident itself. Rather, it shows that attackers do not need to touch a single bedside device to cause serious harm. Instead, they hit makers, logistics firms, remote-access tools, back-office systems, and supplier platforms. As a result, they still produce delay, confusion, and elevated risk across the entire healthcare system.
For hospital leaders and boards, the lesson is clear: healthcare is no longer just a victim of random cybercrime. In a conflict setting, it becomes a deliberate target. This is because disruption in healthcare produces cascading effects that are hard to contain and easy to exploit.
For a closer look at how these risks play out in practice, see the Citanex Case Study: Securing Healthcare in the Digital Age.
Why the Iran Cyber Threat Puts Banks and Financial Firms at Risk
The Iran cyber threat to financial institutions is especially acute. These firms combine symbolic value, systemic weight, and public confidence effects, making them high-priority targets. Even a small disruptive attack on online banking, payment channels, or identity systems can create wide instability.
Importantly, the goal is not always theft. In many cases, the aim is disruption, reputational harm, and loss of trust. Moreover, in the current threat climate, that logic hits financial services especially hard. After all, confidence itself is a fragile and critical asset in this sector.
Other U.S. Businesses Exposed to the Iran Cyber Threat
The targeting logic extends well beyond hospitals and banks. During periods of global tension, hostile actors look for organizations that are important, visible, or simply vulnerable enough to hit hard.
As a result, the likely risk pool is broad. It includes healthcare and life sciences firms, financial services companies, defense-linked businesses, critical infrastructure operators, cloud and tech providers, logistics firms, and smaller entities with fewer resources. In particular, these smaller organizations are at high risk because a breach there can open a door into a much larger ecosystem.
Most Exposed Right Now
- Healthcare systems and suppliers
- Banks and financial institutions
- Critical infrastructure operators
- Defense-adjacent businesses
- Executives with public profiles
- High-net-worth households and frequent travelers

Iran Cyber Threat Actors: State-Linked Groups, Proxies, and Their Targets
Iran’s cyber threat landscape requires careful framing. Attribution varies across public and private reporting. In many cases, operators are better described as state-linked, MOIS-aligned, IRGC-affiliated, or Iran-linked rather than given firm labels.
That said, several groups are consistently relevant when looking at Iranian cyber capability.
| Actor / Alias | Likely Alignment | Primary Objective | Typical Targets | Notable Risk |
| Handala | Iran-linked / pro-Iranian operator | Retaliatory disruption, deletion, and pressure operations | Healthcare-adjacent firms, symbolic retaliation targets | Timely example of healthcare-adjacent cyber retaliation |
| MuddyWater | MOIS-aligned | Espionage, access operations, persistence | Telecom, defense, local government, oil and gas | Broad access into government and commercial networks |
| APT35 / Charming Kitten | State-linked; often associated with Iranian government objectives | Phishing, credential theft, social engineering, espionage | Medical researchers, diplomats, media, government, energy, telecom | High-value targeting of individuals and institutions |
| APT34 / OilRig | Iranian state-linked espionage actor | Espionage, phishing, persistence, supply-chain style attacks | Government, finance, energy, telecom, oil and gas | Exposure across finance and critical sectors |
| APT33 / Elfin | State-linked actor | Espionage, password spraying, destructive tradecraft | Aviation, manufacturing, engineering, energy, petrochemical | Risk to industrial and strategic sectors |
| CyberAv3ngers | IRGC-affiliated persona | Disruptive operations against internet-exposed industrial systems | Water, wastewater, OT / ICS environments | Direct relevance to civilian critical infrastructure |
Attribution note: Public attribution in cyber operations can evolve. This illustration reflects open-source reporting and government or industry assessments available as of March 18, 2026.
Silent Adversarial Parties: The Wider Strategic Ecosystem, Including BRICS-Aligned Dynamics
This issue requires careful framing. BRICS is not a military alliance. In fact, it would be inaccurate to say BRICS as a bloc is running coordinated cyber attacks against the United States.
At the same time, official BRICS documents show a growing structure for cooperation on digital security. This includes working groups, cooperation plans, and proposals for CERT-to-CERT links. Therefore, the more accurate risk framing is this: the United States faces a broader network of aligned, partly aligned, or mutually useful hostile interests. Notably, that network is still growing.
How the Iran Cyber Threat Extends to Cables, Data Centers, and Physical Systems
One of the most damaging myths in cyber risk is that digital attacks are somehow separate from physical systems. They are not. In reality, digital conflict depends on very physical assets. These include undersea cables, landing stations, fiber routes, data centers, cloud regions, and satellites.
For that reason, undersea cables, data centers, and cloud systems must be treated as strategic ground. When hostile actors expand the battlespace, these systems become critical targets. Specifically, they support communications, finance, logistics, and cloud services. Disrupting them produces immediate, far-reaching effects.
The Iran Cyber Threat to Executives, High-Net-Worth Individuals, and Families
In the current Iran cyber threat environment, this risk does not stop at the office perimeter. In fact, in a modern conflict setting, executives and prominent individuals face real risk at work, at home, and while traveling. That risk includes credential theft, phishing, device attacks, surveillance, account takeover, and home network attacks. Additionally, hostile actors target family members, assistants, and household staff as easier entry points.

For executives, board members, and high-net-worth individuals, this is no longer just a workplace security issue. Rather, it is a personal digital risk problem. A hacked home network, personal phone, travel laptop, or family member’s account can become an entry point into business systems.
This is precisely where a Citanex Cyber Threat Intelligence (CTI) report becomes valuable. For an individual or organization, a CTI review identifies sector-specific risk, digital footprint, likely attack paths, and key defensive steps. For higher-risk executives, families, and homes, a broader protective approach may also call for a Citanex Seraphim engagement covering executive, home, and travel-related digital risk.
How the Iran Cyber Threat Reaches Private Homes and Travel Environments
Home environments are increasingly full of connected devices, smart-home tools, cameras, Wi-Fi appliances, and home-office systems. For an executive or high-net-worth individual, this creates a private attack surface. Notably, it is typically less protected and less monitored than the corporate environment.
Travel makes that risk much worse. Devices face exposure to untrusted networks, physical observation, unfamiliar charging setups, hotel systems, and local threat actors. Furthermore, executives and families often carry sensitive access or location data. Hostile actors exploit these through phishing, credential theft, or account takeover.
Compromise can also come through everyday items. For instance, executives who use public or borrowed chargers face risk from tampered cables or cable swaps. These can introduce harmful code, enable remote access, or create a data path once linked to a trusted device. Citanex has covered this risk through its OMG cable video and its article on why iPhones remain high-value targets. The key takeaway is simple: charging cables and adapters must be treated as part of the attack surface during travel and at home.
In short, executive protection today must cover cyber, physical, home, and travel risk together. Treating them as separate issues is no longer a viable approach.
Typical Iranian Tradecraft to Watch
- Spearphishing and fake personas
- Credential harvesting
- Password spraying
- Exploitation of known vulnerabilities
- Web shells and persistence mechanisms
- Destructive or wiper-style effects
- DDoS and psychological disruption
- OT / ICS targeting where civilian impact is high
How to Respond to the Iran Cyber Threat in 2026: What Organizations Must Do Now
Organizations must treat the current climate as a strategic resilience problem, not just an IT issue. In practice, that means hardening internet-facing assets and fixing known weak points. It also means reviewing credential security, checking identity systems, and segmenting critical networks. Most importantly, leaders must know which assets are truly mission-critical before an incident hits, not after.
For executives and high-risk individuals, action is equally urgent. Specifically, they must review home exposure, travel-device hygiene, and family ecosystem risk. They should also assess whether enhanced monitoring or executive-focused CTI support is needed. In a multi-domain conflict setting, the next serious breach may not start in the data center. Instead, it may start with a home network, a travel laptop, a personal inbox, or a trusted third party.

Citanex View: Responding to the Iran Cyber Threat in 2026
Citanex’s position is clear: organizations and individuals must stop treating cyber readiness as a simple compliance task. Instead, they must operate from a risk intelligence, resilience, and continuity model. In the current climate, the risk pool spans enterprise systems, supply chains, executive leadership, private homes, family networks, and travel patterns.
For businesses, that may mean a CTI-driven threat review, external exposure check, executive risk analysis, and resilience planning. For executives, families, and high-net-worth individuals, it may mean asking whether a more protective posture is needed. In that case, Citanex Seraphim covers home, travel, and digital lifestyle environments fully.
Concerned about geopolitical cyber exposure?
A Citanex Cyber Threat Intelligence (CTI) report can help identify sector-specific risk, visible attack surface, and priority actions.
For executives, high-net-worth individuals, homes, and travel environments, Citanex Seraphim provides a stronger protective posture across the modern digital threat surface.
Final Thought: The Iran Cyber Threat in 2026 Has No Boundaries
Iran’s cyber strategy has long relied on asymmetry, denial, proxies, and the use of weak systems to apply pressure efficiently. However, what has changed is the scale of the Iran cyber threat in 2026 and how far it reaches.
Today, the battlespace spans healthcare systems, financial networks, critical infrastructure, digital supply chains, executive lifestyles, home technology, and travel exposure — all at once. Hospitals, banks, businesses, executives, and private homes are not outside that conflict logic. On the contrary, in many cases they are squarely within the target set.
That is the reality of modern conflict: the next strike may not begin with a missile. Instead, it may begin with a hacked account, a dead VPN, a hijacked supplier portal, a wiped device, a manipulated home network, or a travel device that connected where it never should have.